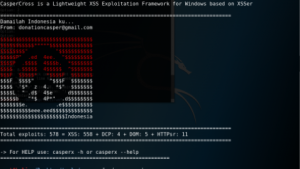
CasperCross – это версия Xsser для Windows.
Автоматическая фрагментация, обнаружение, использование и отчетность уязвимостей XSS на веб-сайте.
Он содержит несколько вариантов обхода защиты XSS и различные пэйлоады.
Сайт проекта: https://xsser.03c8.net
Форум: irc.freenode.net -> #xsser
CasperX работает из коробки с версией Python 2.6.x и 2.7.x, она предназначена для работы на Windows с Powershell, но в основном работает на любой платформе с установленным Python.
Usage:
casperx [OPTIONS] [--all |-u |-i |-d (options)|-l ] [-g |-p |-c (options)]
[Request(s)] [Checker(s)] [Vector(s)] [Anti-antiXSS/IDS] [Bypasser(s)] [Technique(s)] [Final Injection(s)] [Reporting] {Miscellaneous}
CasperCross is a Lightweight XSS Exploitation Framework for Windows based on
XSSer
Options:
--version show program's version number and exit
-h, --help show this help message and exit
-s, --statistics show advanced statistics output results
-v, --verbose active verbose mode output results
--gtk GUI Version will be available soon
--wizard start Wizard Helper!
*Special Features*:
You can set Vector(s) and Bypasser(s) to build complex scripts for XSS
code embedded. XST allows you to discover if target is vulnerable to
'Cross Site Tracing' [CAPEC-107]:
--imx=IMX IMX - Create an image with XSS (--imx image.png)
--fla=FLASH FLA - Create a flash movie with XSS (--fla movie.swf)
--xst=XST XST - Cross Site Tracing (--xst http(s)://host.com)
*Select Target(s)*:
At least one of these options must to be specified to set the source
to get target(s) urls from:
--all=TARGET Automatically audit an entire target
-u URL, --url=URL Enter target to audit
-i READFILE Read target(s) urls from file
-d DORK Search target(s) using a query (ex: 'news.php?id=')
-l Search from a list of 'dorks'
--De=DORK_ENGINE Use this search engine (default: duck)
--Da Search massively using all search engines
*Select type of HTTP/HTTPS Connection(s)*:
These options can be used to specify which parameter(s) we want to use
as payload(s) to inject:
-g GETDATA Send payload using GET (ex: '/menu.php?q=')
-p POSTDATA Send payload using POST (ex: 'foo=1&bar=')
-c CRAWLING Number of urls to crawl on target(s): 1-99999
--Cw=CRAWLER_WIDTH Deeping level of crawler: 1-5 (default 3)
--Cl Crawl only local target(s) urls (default TRUE)
*Configure Request(s)*:
These options can be used to specify how to connect to the target(s)
payload(s). You can choose multiple:
--cookie=COOKIE Change your HTTP Cookie header
--drop-cookie Ignore Set-Cookie header from response
--user-agent=AGENT Change your HTTP User-Agent header (default SPOOFED)
--referer=REFERER Use another HTTP Referer header (default NONE)
--xforw Set your HTTP X-Forwarded-For with random IP values
--xclient Set your HTTP X-Client-IP with random IP values
--headers=HEADERS Extra HTTP headers newline separated
--auth-type=ATYPE HTTP Authentication type (Basic, Digest, GSS or NTLM)
--auth-cred=ACRED HTTP Authentication credentials (name:password)
--proxy=PROXY Use proxy server (tor: https://localhost:8118)
--ignore-proxy Ignore system default HTTP proxy
--timeout=TIMEOUT Select your timeout (default 30)
--retries=RETRIES Retries when the connection timeouts (default 1)
--threads=THREADS Maximum number of concurrent HTTP requests (default 5)
--delay=DELAY Delay in seconds between each HTTP request (default 0)
--tcp-nodelay Use the TCP_NODELAY option
--follow-redirects Follow server redirection responses (302)
--follow-limit=FLI Set limit for redirection requests (default 50)
*Checker Systems*:
These options are useful to know if your target is using filters
against XSS attacks:
--hash send a hash to check if target is repeating content
--heuristic discover parameters filtered by using heuristics
--discode=DISCODE set code on reply to discard an injection
--checkaturl=ALT check reply using: alternative url -> Blind XSS
--checkmethod=ALTM check reply using: GET or POST (default: GET)
--checkatdata=ALD check reply using: alternative payload
--reverse-check establish a reverse connection from target to XSSer to
certify that is 100% vulnerable (recommended!)
*Select Vector(s)*:
These options can be used to specify injection(s) code. Important if
you don't want to inject a common XSS vector used by default. Choose
only one option:
--payload=SCRIPT OWN - Inject your own code
--auto AUTO - Inject a list of vectors provided by XSSer
*Anti-antiXSS Firewall rules*:
These options can be used to try to bypass specific WAF/IDS products.
Choose only if required:
--Phpids0.6.5 PHPIDS (0.6.5) [ALL]
--Phpids0.7 PHPIDS (0.7) [ALL]
--Imperva Imperva Incapsula [ALL]
--Webknight WebKnight (4.1) [Chrome]
--F5bigip F5 Big IP [Chrome + FF + Opera]
--Barracuda Barracuda WAF [ALL]
--Modsec Mod-Security [ALL]
--Quickde
Примечание: Информация для исследования, обучения или проведения аудита. Применение в корыстных целях карается законодательством РФ.